Cybersecurity has become an essential consideration for medtech.
I discussed the basics in my last blog, where I expanded on how increasingly sophisticated cyberattacks and growing connectivity in the medical field meant medical device manufacturers must be aware of cybersecurity at every stage of product development.
My advice to following the relevant legal guidelines and maintaining a proactive approach as outline still stands. But a new year has brought countless new reasons to be on top of cybersecurity, and in this blog, I’ll explain how you should do it.
What’s changed for medical device security?
First and foremost, the nature of risk continues to expand and diversify. Since I wrote last April, even more medical devices are now connected to the internet. An email-launched attack on the Irish HSE last year, which prevented COVID treatment and vaccines from being rolled out, is a clear sign of what can happen when security is insufficient in a highly-connected environment.To mitigate these growing risks, industry security regulation is developing rapidly across the globe. Organizations like NIST in the US and ENISA in the EU are part of a greater movement for a standardized approach to cybersecurity. They promote:
- Clear guidelines to estimate risk
- Compensating controls and litigations for identified issues
- Comprehensive tools to catch and eliminate security flaws, such as static and binary code analysis or penetration testing
This movement is matched by an expansion in guidelines around medical devices more generally. The FDA recently introduced pre-market submission and post-market surveillance requirements, with more information now required for the pre-submission process. In Europe, the EU introduced MDR in May 2021, with a focus on cybersecurity regulation and risk; elsewhere, Canada, China, Australia, and Japan are all introducing similar new legislation.
To summarize, there are now more potential targets, and more regulation to keep abreast of.
What does this mean for medical device companies?
Stricter regulation and diversifying threats mean there’s a need for greater awareness, and a greater response, from the medical device industry.
On top of the existing risks outlined in my previous article, failing to meet guidelines and regulations in any new submissions could mean significant delays in the development and rollout of any new medical device; particularly if supplementary evidence are required to demonstrate cybersecurity compliance. Given that medical device creation can be a lengthy process anyway, further delays only serve to prolong the time to secure ROI.
Yet we mustn’t let fear be the only driver of cybersecurity, be it fear of attacks or fear of delays. It’s true that cybersecurity presents risks, but these can be mitigated with the right approach. Once that approach is put in place, cybersecurity can be a real opportunity for medical device creators to ensure devices are safe from attack in the long-term and that customers and partners can trust you.
So, what does the right approach for medical device vendors look like?
How should you approach medical device cyber security?
Getting cybersecurity right is a case of removing barriers (such as lack of a security process, required technology, or trained experts) and establishing awareness of what you need to do not only to ensure your device is secure but also to provide regulators with all they need to make approval of your device straightforward.
It’s important to remember at this point, that cybersecurity is wide-ranging and complex. It’s not something that you do once and is finished, it’s a cycle that spans the entire lifetime of a product.
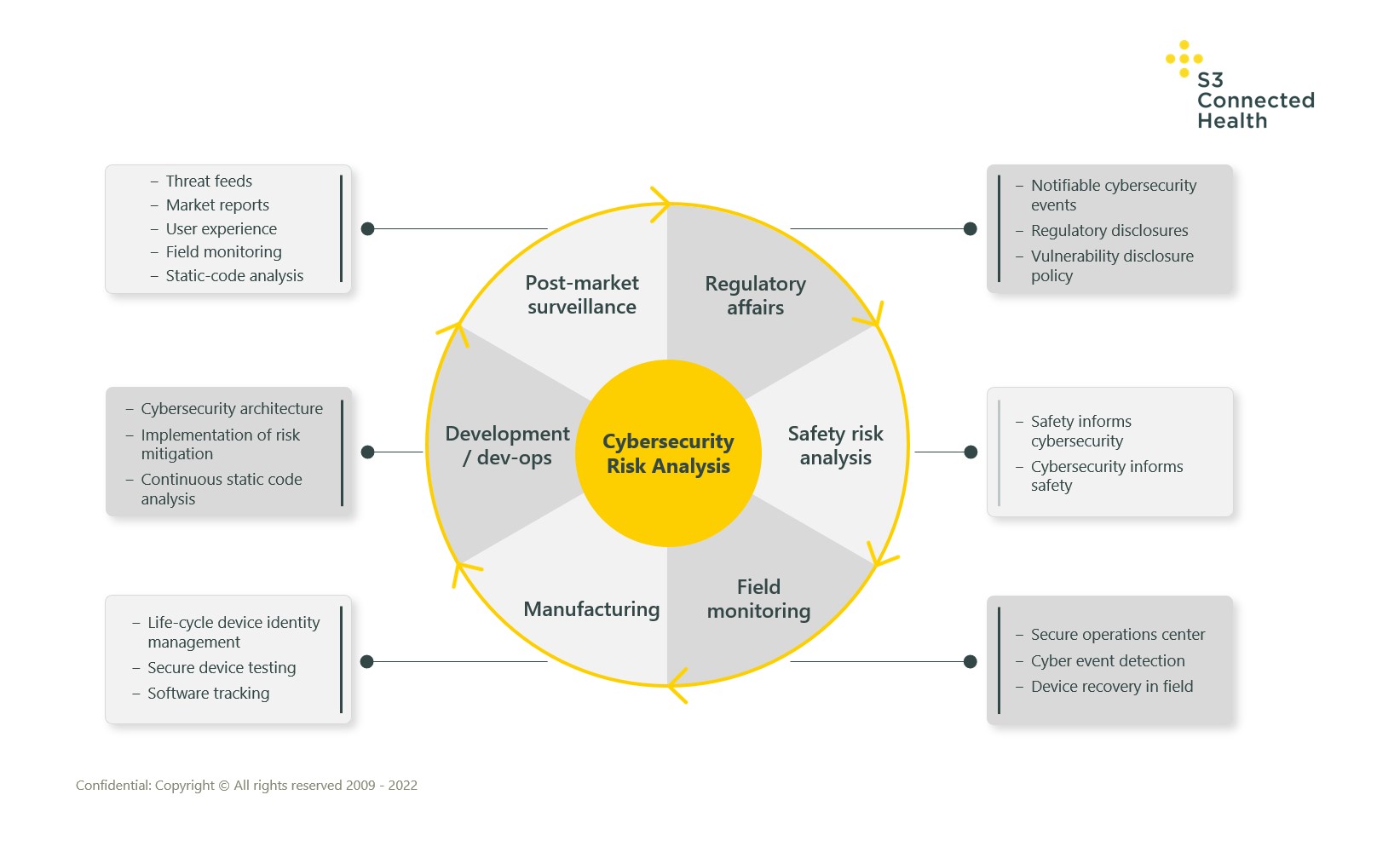
The cycle starts with risk analysis, but this and other activities such as field monitoring and dev ops must be repeated periodically on an ongoing basis. Existing problems must be driven out of the system, emerging ones must be identified, tracked, and eliminated.
The diagram below gives a holistic overview of the key areas of risk analysis in the cybersecurity cycle:
Following the risk-analysis process, how device creators act on the risks they find can be summarized into four main sequential focus areas – we call them security ‘inputs’:
Process
- Establish process in the organization for design, development, testing, and post-market surveillance
Design and Development
- Define the threats to a device, design the architecture and compensating controls
- Build a robust device with the correct compensating controls
Test
- Verify and validate all aspects of the design work from access control and encryption to software signing
Monitor
- Continuously monitor the device to ensure it is operating correctly and respond to potential emerging threats
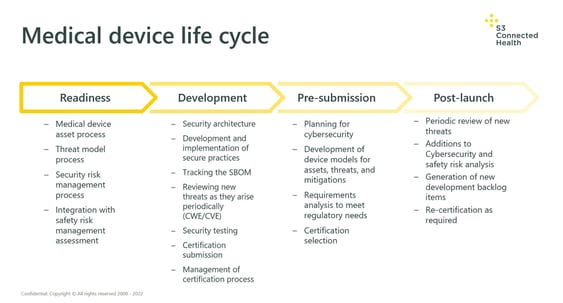
To reiterate: this is a cyclical process that needs to be repeated frequently throughout a product’s life cycle, particularly when new features are added. The diagram below demonstrates what these inputs may look like when the above processes are applied throughout the life cycle of a product:
Think long-term from the start about cyber security
I can’t say it enough: cybersecurity is not a short-term process. It requires constant vigilance and a rapid response when issues are identified.
Adopting a methodical approach turns cybersecurity from a kind of additional, scary ‘chore’ you need to go through to secure regulatory approval into part of the regular cadence of updates that every device needs to keep it up-to-date and running smoothly.
If there’s even the slightest chance a new device that you’re creating may one day be connected, complete the relevant cybersecurity checks upfront to make it quick and easy to secure additional certification as required.
When cybersecurity is integrated from the start of the device creation, you shorten the development process and protect against any vulnerabilities to any would-be attackers. That means your devices remain secure, and you can keep the trust of partners, customers, clinicians, and patients.

To learn how to make your medical device more adaptable to deliver value into the future, download the full whitepaper now and gain free, immediate access.